Deterministic Transactional Integrity
Runtime Enforcement for Safe Agentic Financial Transactions
Section 1 — The Executive Problem: Probabilistic Liability
Agentic Systems Create Transactional Liability
Autonomous AI agents are increasingly authorized to initiate payments, approve disbursements, move funds between accounts, and execute financial commitments on behalf of organizations. These agents operate on probabilistic outputs — language model completions that are statistically likely but never deterministically correct. When a probabilistic system controls real money, every transaction carries an implicit liability that no monitoring layer can eliminate after the fact.
Why Monitoring Cannot Solve This
Observability tools detect anomalies after funds have already moved. Alerting systems notify operators after unauthorized spend has already occurred. In financial operations, the distinction between detection and prevention is the distinction between loss recovery and loss avoidance. Recovery is expensive, uncertain, and reputationally damaging. Avoidance is an architectural property.
The Core Shift
HALMAI moves agentic financial systems from probabilistic safety to deterministic enforcement. Every payment action proposed by an agent is evaluated against policy, authorized or denied at the kernel level, and cryptographically recorded — before any funds move.
The Consequence of Ungoverned Payment Agents
Without a runtime enforcement layer between the agent and the payment gateway, autonomous systems operate with implicit treasury access. A single prompt injection, misconfigured policy, or runaway loop can result in:
- Unauthorized disbursements exceeding budget envelopes
- Payment routing to unverified or adversarial counterparties
- Recursive transaction patterns draining treasury before detection
- Compliance violations with no auditable decision trail
Section 2 — Architecture: The Enforcement Rail
Where HALMAI Sits
HALMAI is positioned between agentic intent and real-world execution — between any autonomous action and its side effect. Framework-agnostic and target-agnostic, no action reaches the payment processor, database, API endpoint, or external system without first passing through the HALMAI enforcement kernel. This is not a middleware suggestion. It is the only code path to execution.
Proposal → Authorization → Execution
Every agentic payment action follows a strict three-phase boundary:
Proposal
Agent generates a transaction intent — payment type, amount, counterparty, and context. The proposal is structured, not free-text.
Authorization
The enforcement kernel evaluates the proposal against active policy rules. Returns ALLOW, DENY, or LOCKDOWN. No ambiguity.
Execution
Funds move only through the secure executor with a valid, single-use, cryptographically-bound execution token.
Side-Effect Isolation
All action types with financial consequences are registered in a typed side-effect catalog. The catalog defines required authorization levels, budget categories, and counterparty verification rules for each action type. Unregistered action types cannot execute. This prevents agents from discovering novel paths to move funds outside the enforcement boundary.
Budget Envelopes and Circuit Breakers
Every tenant operates within configurable budget constraints. The kernel tracks spend per action type, per time window, and cumulatively. Hard caps are enforced at the authorization layer — agent logic cannot override them. When cumulative spend approaches or breaches a threshold, the circuit breaker triggers automatic lockdown: all payment execution halts, and manual intervention with logged justification is required to resume.
Example Budget Configuration
Daily Spend Cap
$50.00
Single Transaction Max
$25.00
Velocity Limit (per hour)
10 txns
Breach Response
Lockdown
Lockdown Protocol
Lockdown is not a suggestion or an alert severity level. When invariant violations, budget breaches, or adversarial patterns are detected, all payment execution halts immediately and system-wide. No agent can bypass a lockdown. Restoration requires authenticated human intervention with a logged justification that becomes part of the permanent audit record.
Runtime Architecture
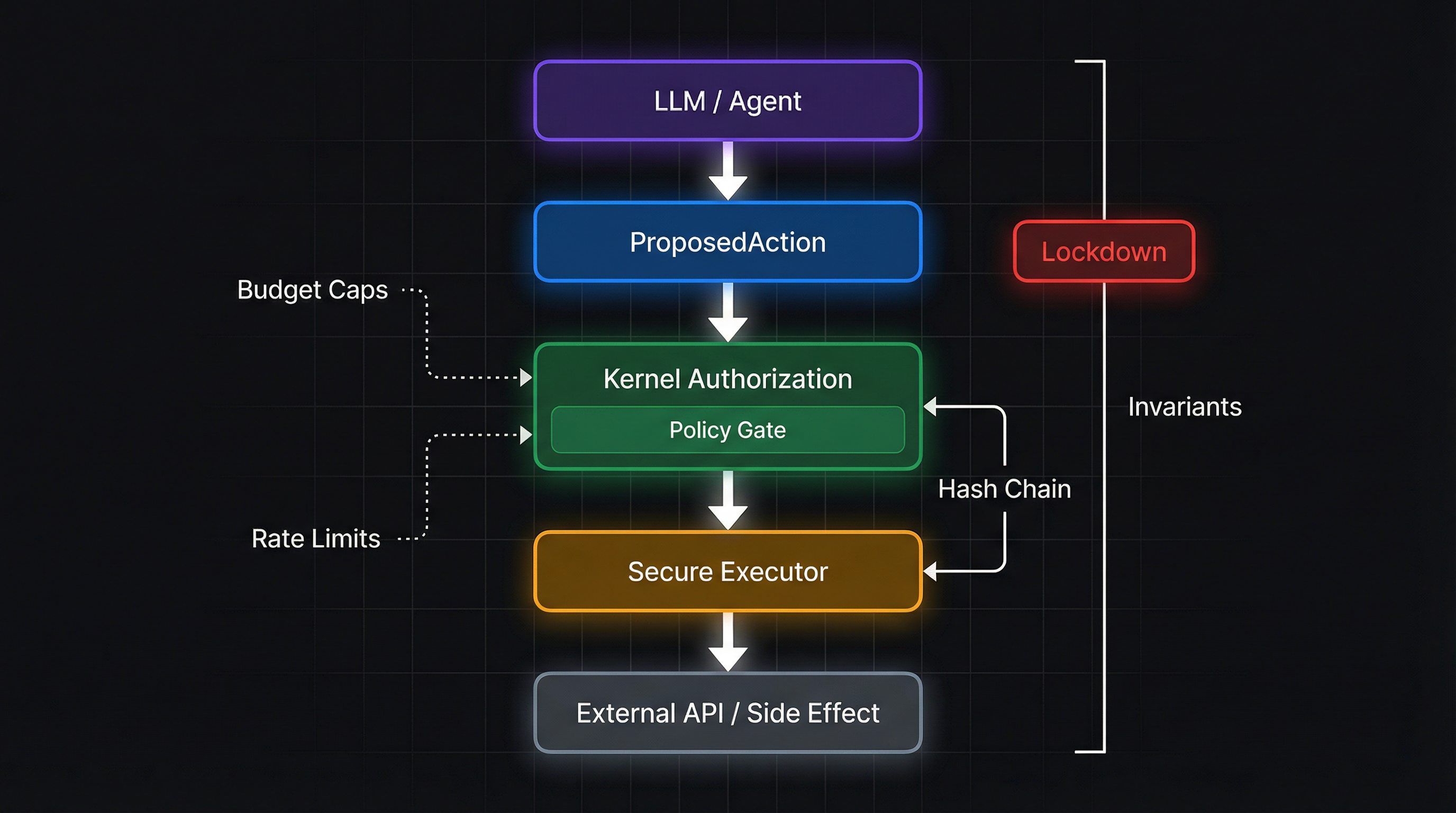
Figure 1: Runtime Enforcement Architecture — The deterministic boundary between agentic intent and financial execution
Section 3 — Validation Framework
What the Proof System Enforces
HALMAI produces cryptographic proof artifacts for every authorization decision. These are not abstract verification scores or statistical confidence intervals. Each proof is a concrete, independently verifiable record that a specific transaction was evaluated against a specific policy state and produced a specific enforcement outcome — authorize, deny, or lockdown. The proof binds the decision to the policy version, the proposal payload, and the timestamp, making post-hoc modification detectable.
Hash-Chained Decision Ledger
Every authorization decision is recorded with a cryptographic hash linking it to the previous decision. This creates a tamper-evident chain where any modification — insertion, deletion, or alteration — breaks the hash continuity and triggers an integrity violation. The ledger is append-only. Only the secure executor context can write to it. Direct database writes to protected tables are blocked by runtime middleware.
Replay Under Historical Policy State
Policy rules are stored with full version history. Each modification creates a snapshot preserving the complete rule state at that moment. Given any historical transaction and the policy version that was active when it was evaluated, the authorization decision can be replayed deterministically. The replay mechanism proves that:
- The recorded decision matches what the rules would produce today for that input
- No manual override or post-hoc tampering altered the outcome
- The enforcement kernel behaved consistently across all evaluated transactions
# Replay verification endpoint
POST /api/policy/replay
{"proposalId": "prop_abc123", "ruleVersion": 42}
→ Returns: decision match status, hash verification, discrepancies if any
Audit-Grade Evidence
The combination of hash-chained decisions, versioned policy snapshots, and deterministic replay produces evidence that meets the evidentiary standards required by financial auditors, compliance officers, and regulators. This is the operational definition of Deterministic Transactional Integrity: each transaction carries a self-contained proof bundle — the proposal, the policy state, the decision, and the cryptographic linkage to the chain.
Trust Relevance: Underwriters, Boards, and Enterprise Buyers
This validation framework is designed for the stakeholders who bear fiduciary responsibility for agentic financial systems:
- Insurance underwriters — verifiable enforcement posture reduces exposure and supports premium calculation against demonstrable controls, not self-reported questionnaires. A structured Underwriter Evidence Export is on the product roadmap to deliver packaged proof bundles directly to underwriting workflows.
- Boards and audit committees — deterministic proof that every agentic transaction was policy-evaluated, with tamper-evident records suitable for quarterly risk reporting
- Enterprise procurement — standardized governance scores and exportable audit trails for vendor due diligence and compliance attestation
- Regulators — reproducible decision logic with full version history, satisfying requirements under frameworks like NIST AI RMF, EU AI Act, and SOC 2
Kernel Invariants
Six core invariants define the foundational properties of the enforcement system. These are not configurable — they are structural guarantees that must hold for the system to be considered operational. Continuous verification ensures any violation is detected and escalated immediately:
- No financial side effect without an explicit ALLOW decision
- Cryptographically-bound execution token required for all payment actions
- Decision hashes independently verifiable
- Hash chain continuous — no gaps, no insertions
- Lockdown overrides all execution unconditionally
- Tenant isolation enforced at the kernel level
Section 4 — Fiduciary Safety vs. Cybersecurity
Two Distinct Problems
Cybersecurity protects keys, credentials, and system boundaries. It prevents unauthorized actors from accessing infrastructure. Fiduciary safety is a different problem entirely: it protects intent, treasury, and transaction boundaries when the actor is authorized but the action is not. An AI agent with valid API credentials initiating an unauthorized payment is not a cybersecurity breach — it is a fiduciary failure.
What Cybersecurity Covers
Traditional security infrastructure handles authentication, network perimeter defense, encryption at rest and in transit, access control lists, and intrusion detection. These are necessary but insufficient for agentic financial systems. A properly authenticated agent with valid credentials can still execute transactions that violate policy, exceed budgets, or route funds to unauthorized counterparties. Cybersecurity answers the question: is this actor permitted to be here?
What Fiduciary Safety Covers
Fiduciary safety answers a different question: is this specific transaction permitted under current policy, within current budget constraints, and consistent with the organization's financial controls? It operates at the transaction level, not the session or network level. It evaluates intent, amount, counterparty, velocity, and cumulative exposure — per action, in real time.
Cybersecurity
- Protects keys and credentials
- Defends network perimeters
- Enforces access control
- Detects intrusions
- Scope: system boundaries
Fiduciary Safety
- Protects intent and treasury
- Enforces transaction boundaries
- Evaluates per-action policy compliance
- Prevents authorized-but-unauthorized spend
- Scope: every financial action
Why Both Are Required
An agentic payment system secured only at the network level has strong walls and no internal controls. An agentic payment system with fiduciary safety but no cybersecurity has internal controls that an external attacker could disable. Production-grade agentic financial infrastructure requires both: cybersecurity to protect the perimeter, and fiduciary safety to govern every transaction that occurs inside it.
HALMAI's Position
HALMAI is a fiduciary safety layer. It does not replace firewalls, IAM systems, or encryption infrastructure. It sits inside the authenticated boundary and enforces transaction-level policy on every agentic financial action. It is the control surface that answers: given that this agent is authenticated, should this specific payment be authorized right now, under current policy, within current budget?
HALMAI is the runtime enforcement rail for safe autonomous agent actions.
Framework-agnostic. Target-agnostic. The deterministic boundary between agentic intent and real-world execution — authorization, denial, lockdown, and proof for every autonomous action.